Award-Winning Antivirus Software
Norton AntiVirus Plus gives you multi-layered virus and malware protection, plus 24x7Δ member support.

Norton AntiVirus Plus gives you multi-layered virus and malware protection, plus 24x7Δ member support.
Norton AntiVirus Plus
Our powerful antivirus now comes with Genie Scam Protection - AI-powered scam detection that outsmarts hidden scams before they strike.
Free Trials
Get a free trial of Norton protection for PC, Mac, Android or iOS.

How do antivirus apps and antivirus software work?
Antivirus scans and helps remove malware files that enter a computer, tablet or smartphone. Norton AntiVirus technology uses machine learning to determine if a file is good or bad, and can do so even if it’s the first time seeing that file.
Norton protection also uses “emulation” (running each file in a lightweight virtual machine) to cause online threats to reveal themselves – this happens in milliseconds as you double-click on files on your desktop. File signature data is now stored in the cloud, and Norton protection has undergone hundreds of optimizations on the antivirus engine to minimize impacting the user experience.
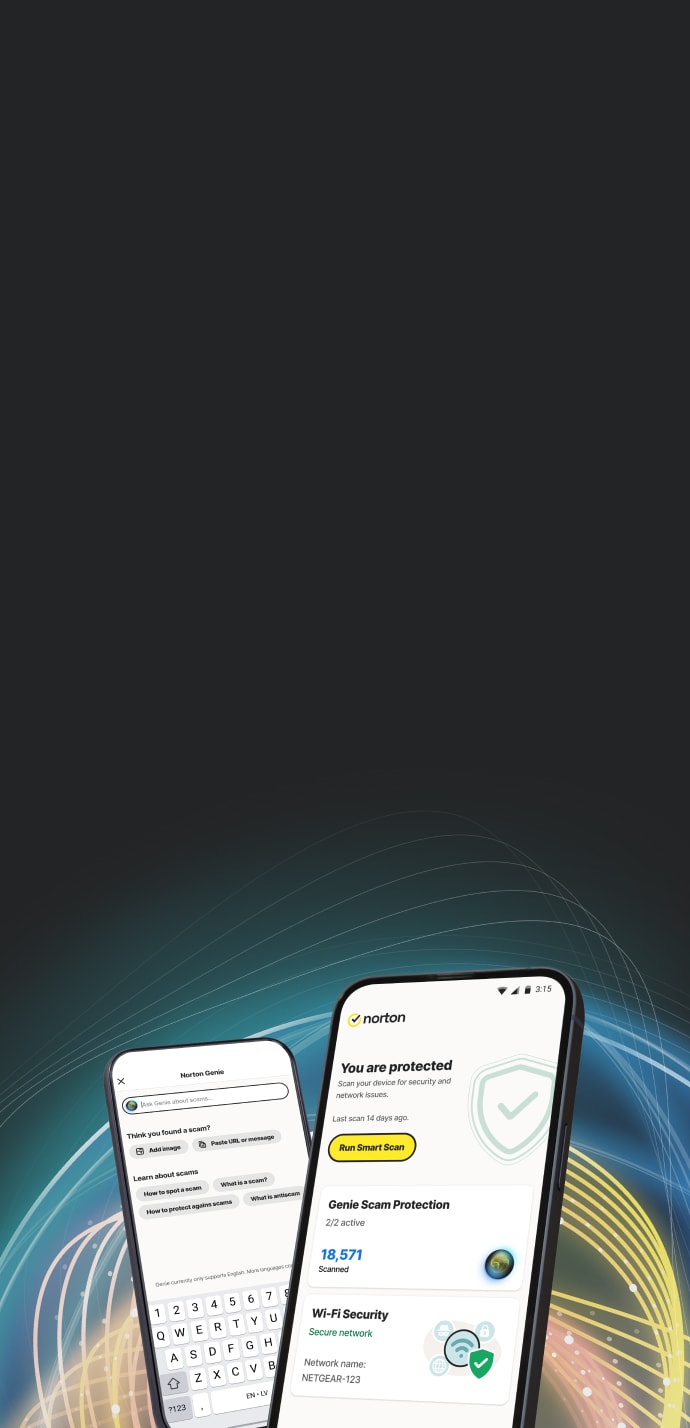
Genie Scam Protection
Every Norton 360 plan now includes Genie Scam Protection, AI-powered detection for advanced scams.
Norton security technology includes multiple defenses against viruses and malware and our technology is powered by artificial intelligence (AI) and machine learning. Our protection includes:
What does Norton antivirus and security software help protect against? Today’s online threats go well beyond just viruses. AntiVirus and malware protection from Norton LifeLock helps defend against all kinds of online threats, such as:
Viruses
Norton protection helps block harmful software that replicates itself and spreads itself to other devices.
Worms
Norton protection helps block malware that replicates itself without using a host file (unlike viruses, who use a file).
Malware
Norton protection has defenses for various types of malicious software, including viruses, Trojans, worms, etc.
Ransomware
Norton protection helps protect against malware that encrypts a computer’s contents and then demands a ransom to restore them.
Spyware
Norton protection detects software that tracks and sends personally identifiable information or confidential information to third parties.
Adware
Norton protection helps block malware that’s designed to display unwanted advertisements.
Think you have a virus? Try these tools:
Need help? Member Services and Support can assist.
How do free antivirus programs compare? Is free antivirus safe?
It’s often said, “you get what you pay for.” The best value in antivirus software is a solution from a trusted provider that offers robust, effective virus and malware protection technology backed by readily available support experts who can help you when you need it.
*Terms apply. For cancellation, return and refund information, please visit the Return Policy.

Antivirus for Windows®
Norton was one of the first antivirus solutions for Windows computers, and we’ve been innovating for decades to develop new ways to help protect PCs. Today, the antivirus protection in Norton solutions uses advanced machine learning and emulation to determine whether files are good or bad, but Norton device security also has more ways to help protect your computer beyond antivirus.
Protection for PCs starts at the network-level, with Intrusion Prevention working together with the Smart Firewall to analyze network traffic and help block potential online threats before they get on your computer.
The technology that powers Norton protection for PC uses Reputation Protection (Insight) to analyze reputation data, a tool that uses the reputation information gathered from our global network to classify software application files. It includes Behavioral Protection to monitor and help block applications that exhibit suspicious behavior, also based on the learnings from our huge trove of data, and tools to help protect against “zero-day” attacks that exploit vulnerabilities in applications or the operating system.

Antivirus for Mac®
Mac computers can get viruses and need file-based antivirus protection. Additionally, they need the other layers of protection offered in a device security software suite such as Firewall, Intrusion Prevention and Anti-phishing Protection.
We have been helping to protect Mac computers for decades. Today, our advanced security and 24-hour threat monitoring across the globe work to outsmart cybercriminals and help stop the latest attacks before they reach your Mac.

Antivirus for Android®
Norton protection for Android includes an array of features and tools, including App Advisor+, Wi-Fi Security, Web Protection, and Safe Search. The app also includes a security Report Card and Anti-Theft tools.
App Advisor+, powered by Norton Mobile Insight, scans apps before you download them and warns you about risky apps before you install them. App Advisor+ for Google Play tells you about malware, online privacy and other risks that are detected for a given app before you choose to download it.

Antivirus for iOS®
Yes! If you log into email or use public Wi-Fi, online threats may get into your iPhone® or iPad®. Your iPhone and iPad carry a lot of important information, and you use them for many different tasks. Norton protection for iOS helps protect your iPhone and iPad with Wi-Fi Security, Web Protection, and Device Security.
Wi-Fi Security helps detect and alert you if your device is connected to a Wi-Fi network that is under attack by cybercriminals, which could lead to someone else accessing your device. Web Protection helps detect and safeguard you from navigation to malicious websites, and Device Security alerts you when your operating system is out of date, which could leave your device susceptible to vulnerabilities.
Antivirus, malware protection, and more features to help protect your device
Norton AntiVirus Plus and Norton 360 plans include antivirus and malware protection, plus an array of additional features to help protect your PCs, Mac, Android and iOS devices, including:

We provide 60 Day Money Back Guarantee* with annual subscriptions.
Norton AntiVirus Plus
Powerful protection for your device and personal information on it.
Norton 360
Get comprehensive protection for your devices.
*Terms apply. For cancellation, return and refund information, please visit the Return Policy
Antivirus is an important part of what you might call internet security, security software or device security. A security solution includes antivirus as one of the foundations of how it helps defend against malware, but “internet security” typically refers to a software suite that has additional types of technology in addition to antivirus.
A computer, tablet or smartphone that connects to the Internet has the potential to encounter viruses and malware. While you may be careful what you do online, you could still visit a website that has been compromised with malware (without even knowing it) or download malware from a message from a trusted friend whose account was hacked. Someone else who uses your device might not be as careful as you. Having antivirus and security software for your computer or mobile device gives you protection against many types of malware that might not be easy to spot.
Antivirus and security software will include a scanning function to check for viruses and malware.
Antivirus and security software will include tools for virus and malware removal. Norton subscribers can also contact Member Services & Support if you think you have a virus or malware.
+ Premium Features
To learn more about features included in the free version of Norton Mobile Security click here
2 Restrictions apply. Must have an automatically renewing device security subscription with antivirus for the virus removal service. See Norton.com/virus-protection-promise for complete details.
Δ 24/7 Support is available in English only. See https://www.norton.com/globalsupport. Identity Restoration Support is only available 9:00 - 18:00 GMT (Mon-Fri), as they are not available 24/7.
‡‡ Requires your device to have an Internet/data plan and be turned on.
The Norton brand is part of Gen.
Copyright © 2025 Gen Digital Inc. All rights reserved. Gen trademarks or registered trademarks are property of Gen Digital Inc. or its affiliates. Firefox is a trademark of Mozilla Foundation. Android, Google Chrome, Google Play and the Google Play logo are trademarks of Google, LLC. Mac, iPhone, iPad, Apple and the Apple logo are trademarks of Apple Inc., registered in the U.S. and other countries. App Store is a service mark of Apple Inc. Alexa and all related logos are trademarks of Amazon.com, Inc. or its affiliates. Microsoft and the Window logo are trademarks of Microsoft Corporation in the U.S. and other countries. The Android robot is reproduced or modified from work created and shared by Google and used according to terms described in the Creative Commons 3.0 Attribution License. Other names may be trademarks of their respective owners.