New study finds 8 social media phishing attacks
Are you active on social media? You could be a target for social media phishing attacks designed to steal your private information.

Here's what you need to look for to help keep your information safe.
Are you active on social media? You could be a target for social media phishing attacks designed to steal your private information.
That’s one of the findings of a new study by Norton Labs. The Labs team analyzed a full year of phishing attacks against social media websites, including Facebook, Instagram, TikTok, Twitter, LinkedIn, and Snapchat.
Among the study’s key findings:
- Phishing campaigns targeting social media use diverse stories to trick a user.
- Facebook is the No. 1 target, with nearly three-of-four phishing websites imitating that platform.
- Social media attacks have become more sophisticated, aided by tools that make campaigns more convincing and easier to unleash.
We take a closer look at each lure with examples below, but first, here is a look at what’s driving the attacks.
Why do scammers target social media?
Social media connects people around the world. Platforms like Facebook, Instagram, TikTok, Twitter, LinkedIn, and Snapchat are often used to interact with friends and colleagues. They’re also used as a tool for accessing news, purchasing products, finding a job, watching videos, and much more.
There are billions of people using social media worldwide, sharing their personal information, such as where they live, what they like, what they are interested in, and who they interact with. Users’ data provides social media companies with information, which allows advertisers to target specific audiences with marketing they think will be effective on that specific group.
For these same reasons, threat actors like social media too. The platforms have become one of the main targets for phishing attacks in recent years and represent a low-effort way to target billions of people anywhere in the world.
And the attacks have become easier. Tools are available that allow a threat actor to easily impersonate known profiles and gain the trust of the victims, which allow the attacks to quickly spread through a list of friends of a compromised account.
The phishing lure list: Watch out for these eight social media phishing tricks
Here’s a closer look at the eight lures we detected, with real-world examples and context. These are all phishing pages; none from the official company that they are pretending to be.
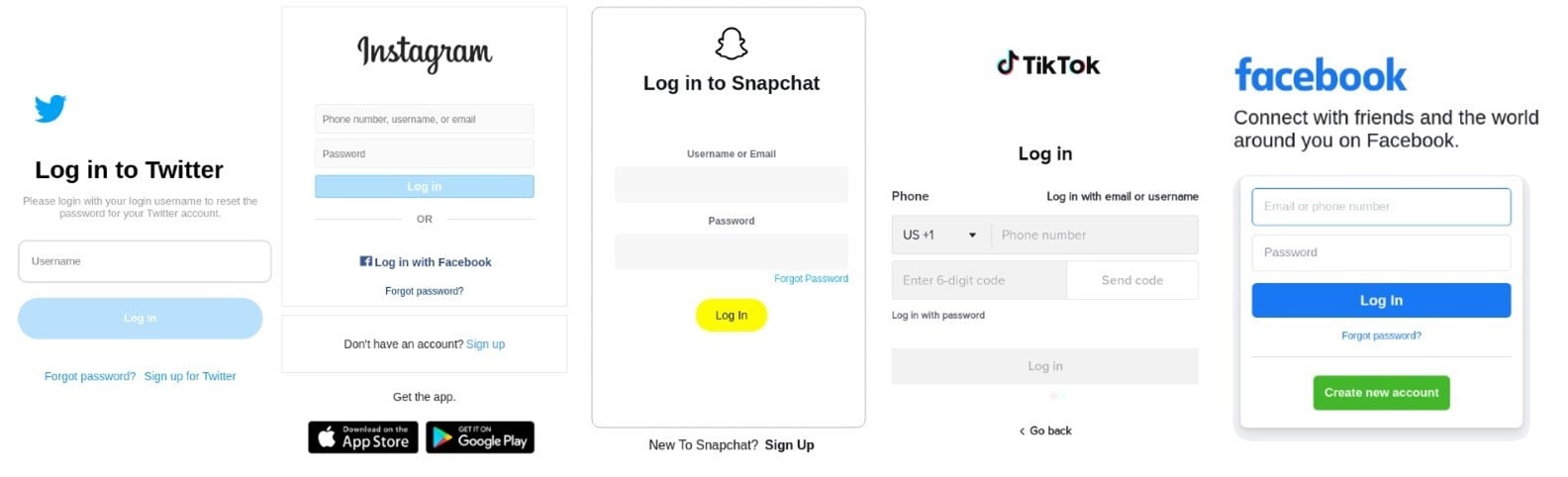
1. Classic login phishing
The creation of a website that is similar in name and appearance to the official social-media login page represents the most common and widespread phishing scheme. This template is used to fool users into believing that the page is legitimate, and to steal their credentials once they try to access their profile.
2. Locked accounts notices
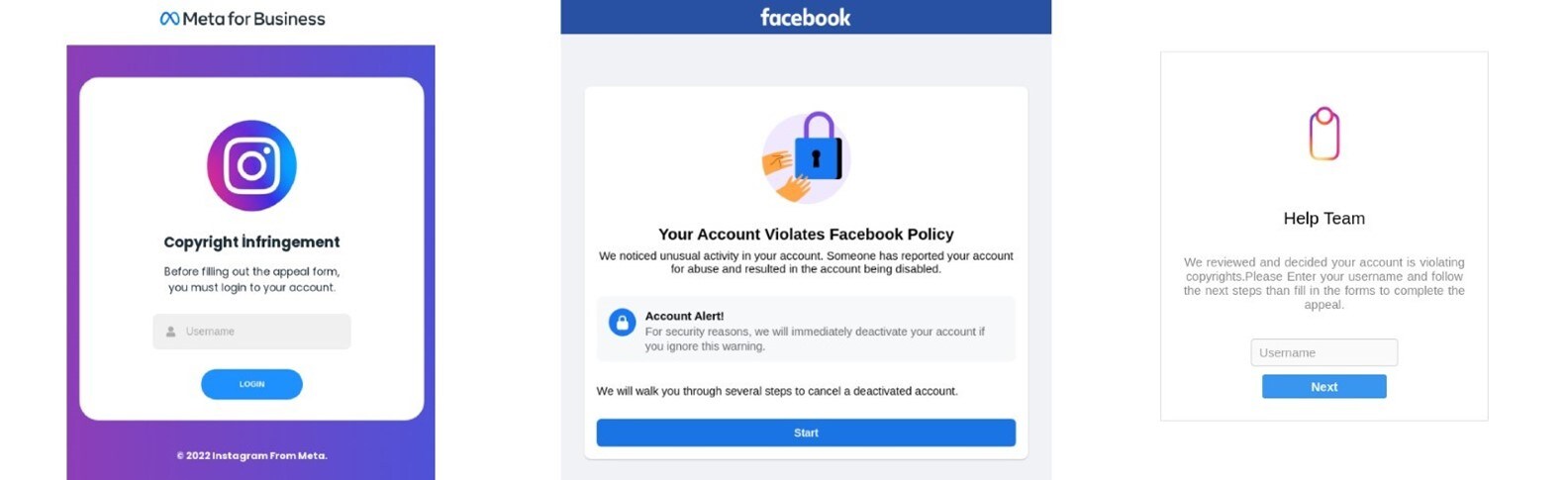
This attack scheme exploits users’ fear of losing access to the account to steal access credentials. Phishing websites of this kind usually intimidate consumers to reveal sensitive information by reporting a (fake) nonauthorized access to their account, the presence of outdated information, or the need to go through a security checklist.

3. Copyright violation notices
Social platforms are not authorized to post material without permission from the copyright holder and have stringent rules to restrict its users from posting a third party’s copyrighted material. Such a clause is leveraged in phishing attacks to deceive users and pretend that the victim’s account has been locked because they violated copyright rules. With this kind of malicious website, victims are required to log in and disclose their credentials to unlock their profiles.
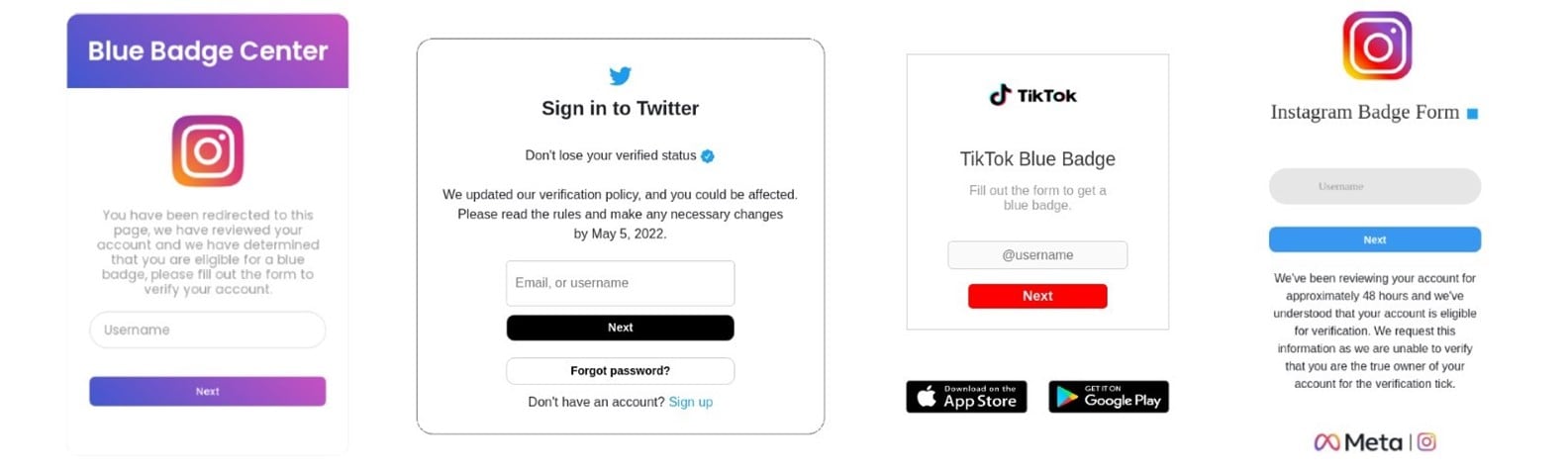
4. Verified badge scams
Verified badges are icons that appear on some social media sites to indicate that the platform has confirmed that an account is the authentic presence of the public/popular figure, celebrity, or brand it represents. Generally, accounts that have been verified are more trusted and may get other advantages like a broader reach. Phishing campaigns use verified badges to lure users into providing login details to the target site. Malicious pages present users with a prompt that asks users to login to obtain, or not to lose, their verified status on the platform.
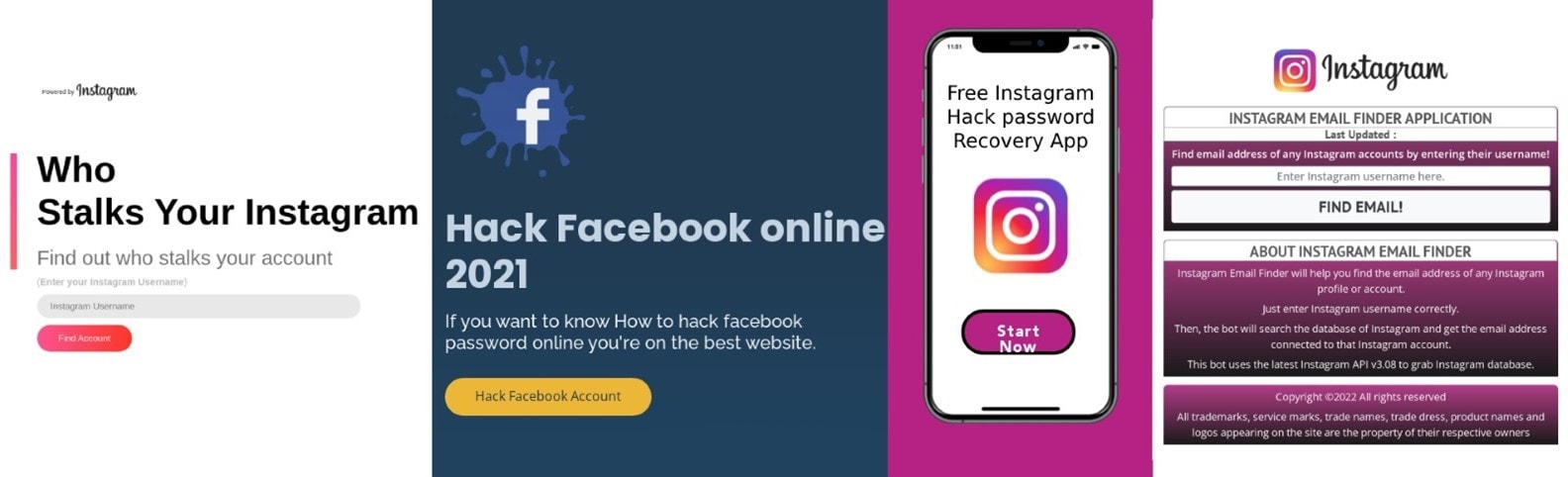
5. Profile hacking services
Profile hacking services represent a recent variant of phishing attacks targeting social media. Malicious campaigns based on hacking services often pretend to offer users a way to hack into a profile or to reveal other customers’ information such as email addresses or their list of interactions. In most cases the goal of these campaigns is not to steal credentials, but to continuously redirect victims and monetize from other services such as ads or surveys.
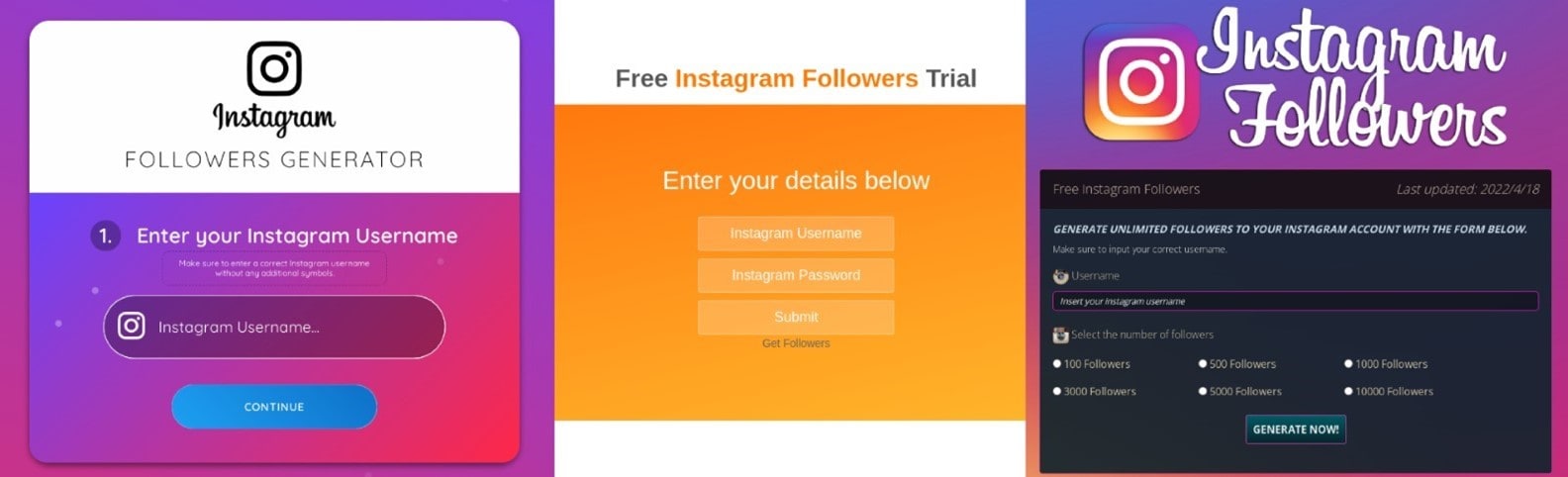
6. Follower generator services
Generating followers and post interactions around social media accounts is one of the main goals of content creators and profile holders. Such an aspect is leveraged by another phishing scheme that promote services to do so at a low or no cost at all. Such attacks can yield profit by redirecting victims to some attacker-controlled websites that display ads (left image), can lure users to reveal login credentials (center image), or can facilitate the spread of malicious software that victims are required to install (right).
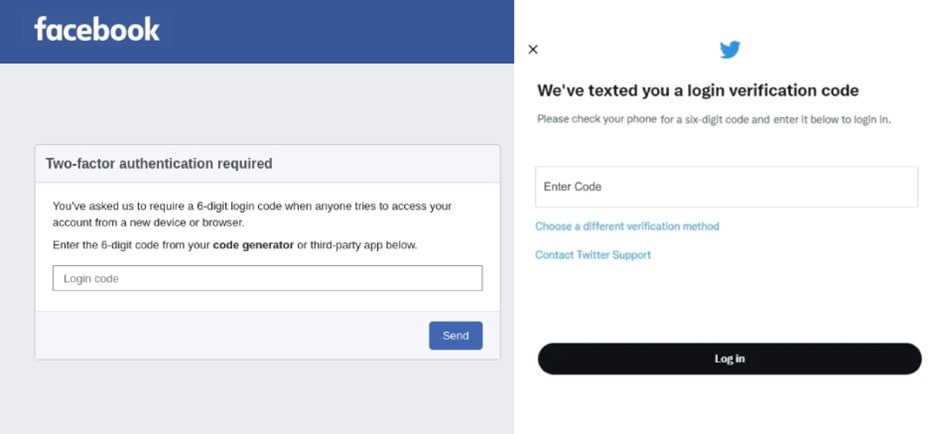
7. Two-Factor authentication interception
While many users are already familiar with two-factor authentication, it might surprise them to learn that their two-factor authentication codes from an app or SMS can also be captured via phishing. For those already familiar with logging in with a two-factor code, a phishing site prompting them for a code just follows a learned log-in behavior.
Sneaky phishing campaigns aim instead to intercept temporary codes to break into profiles with two-factor authentication enabled. Those tokens are generally tied to the victim’s phone number or a code generator app on their device and are typically required to login and make changes to an account
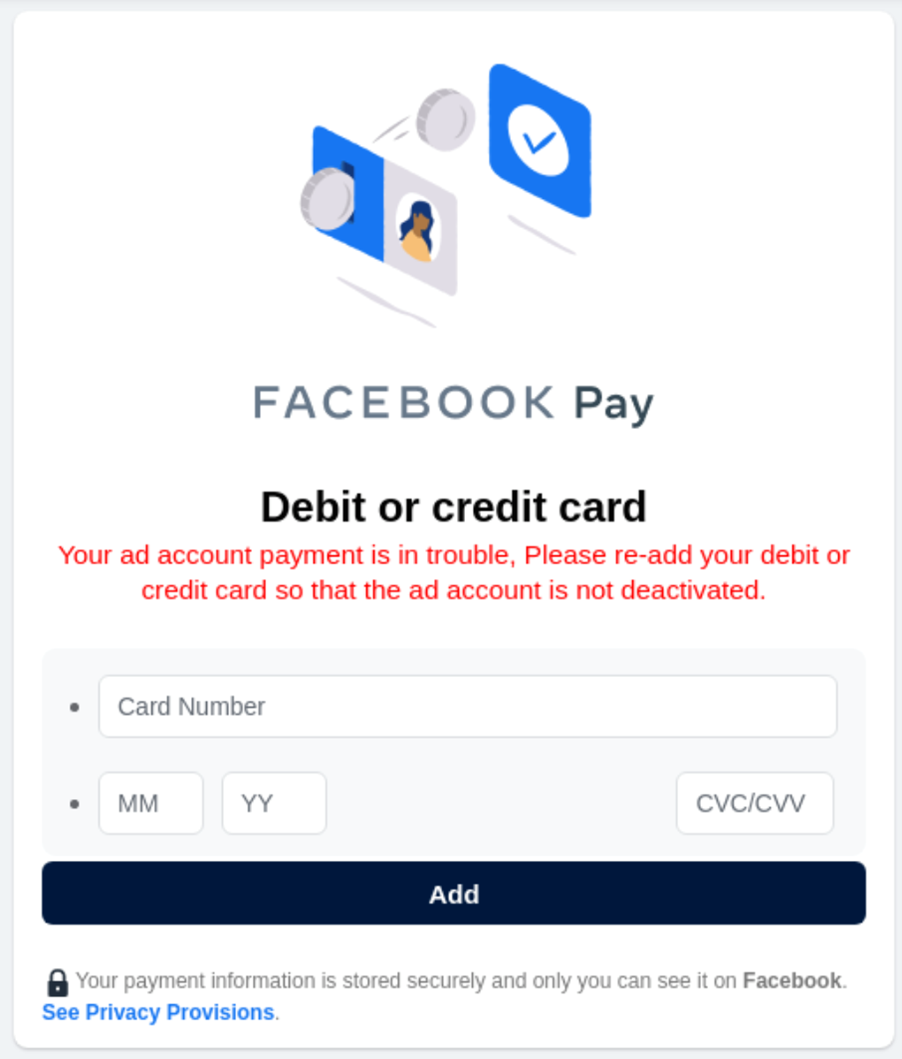
8. Payment fraud
Threat actors also design phishing campaigns that involve social media platforms and at the same time are conceived to steal financial information from the users. Malicious websites usually exploit known social media brands and ask for credit card details from their victims by simulating a problem with their account.
Wrap up
The reason these lures matter is because they have an impact beyond revealing your login information for one company or service. They can take a financial toll on the victim or their contacts, are used to further spread the phishing campaign, and much more. Scammers are trying so hard to get people to reveal their login details, which is why you should be on the lookout for these scams as well as whatever they come up with next.
Editors' note: Our articles offer educational information and are written to raise awareness about important topics in Cyber Safety. Norton products and services may not protect against every type of threat, fraud, or crime we write about. For more details about how we research, write, and review our articles, see our Editorial Policy.





Want more?
Follow us for all the latest news, tips and updates.